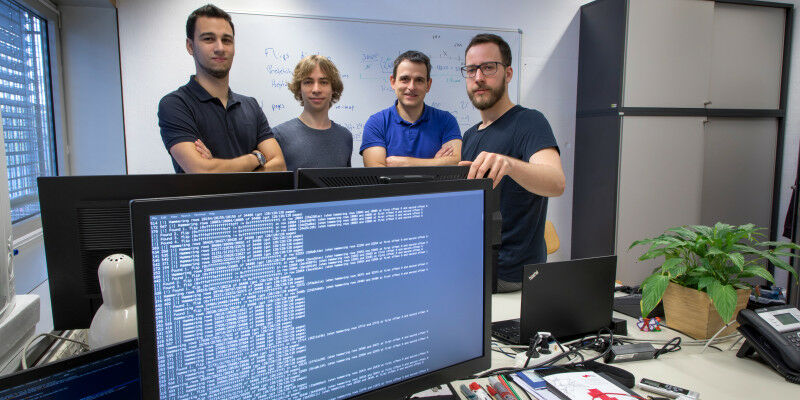
 The research team with Michael Schwarz, Daniel Gruss and Moritz Lipp as well as working group leader Stefan Mangard.
The research team with Michael Schwarz, Daniel Gruss and Moritz Lipp as well as working group leader Stefan Mangard.
Rowhammer attacks make use of hardware vulnerabilities in order to access computer systems. TU Graz researchers have discovered a new type of attack - and raise questions about protective mechanisms. "When a system is regarded as absolutely safe, our curiosity is awakened," explains Daniel Gruss from the Institute of Applied Information Processing and Communication Technology working group, the researcher is occupied with the security of IT systems and in particular rowhammer attacks. Together with colleagues Michael Schwarz and Moritz Lipp, he has recently published research results which have generated excitement in the community to say the least and possibly may lead to a complete rethink. Rowhammer attacks were first recognised as a security problem and scientifically investigated in 2014. Attackers exploit vulnerabilities in the hardware to gain access to computer systems. The security holes are not real hardware faults, but rather come about because the DRAM modules in our computers - the memory - are becoming increasingly smaller.
TO READ THIS ARTICLE, CREATE YOUR ACCOUNT
And extend your reading, free of charge and with no commitment.
Your Benefits
- Access to all content
- Receive newsmails for news and jobs
- Post ads